3 Cloud Security Issues You Can Encounter

What are some cloud security issues you can encounter? Misconfiguration of settings Endpoint user error Cyber threats Due to the flexibility, scalability, and mobility that cloud platforms give, numerous companies are migrating their workloads from on-premises data centers. Cloud providers invest a huge amount of money in research and development to implement better security than […]
Microsoft Azure: an Affordable and Flexible Infrastructure in the Cloud for Businesses
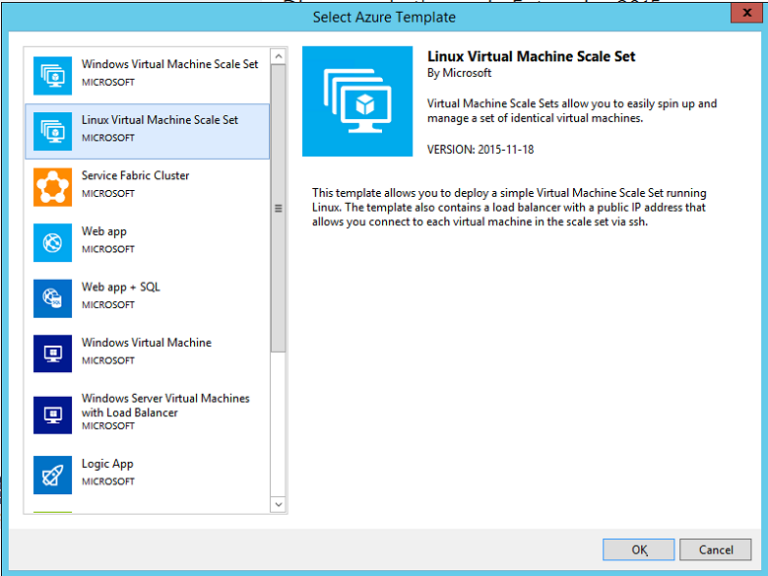
Getting a business started from scratch can be difficult, then adding into the equation of your internal infrastructure? Now that can be a real challenge for some, even daunting. Not knowing exactly what specifications you would need at first for servers can be costly, though this can’t be helped as requirements can be grow as […]
Join Our Upcoming Event Pushstart!
Cloud technology is being used more by many companies due to its operational and economic benefits it can provide to them. This in turn puts more importance into securing your virtualized data centers, cloud deployments and hybrid environments. Leaving any gaps or neglecting any aspect in your security can now expose you and your company […]
