Security Advisory: Meltdown & Spectre Zero day Vulnerabilities
Over the past few days, you may have heard of the new vulnerabilities that has been uncovered, Meltdown and Spectre. These vulnerabilities affect all modern processors, meaning your business machines and even personal gadgets that use processors are affected which puts you in risk of potential attacks. Below is a brief explanation of what exactly […]
Security Advisory: WannaCry Ransomware Attacks (2017)
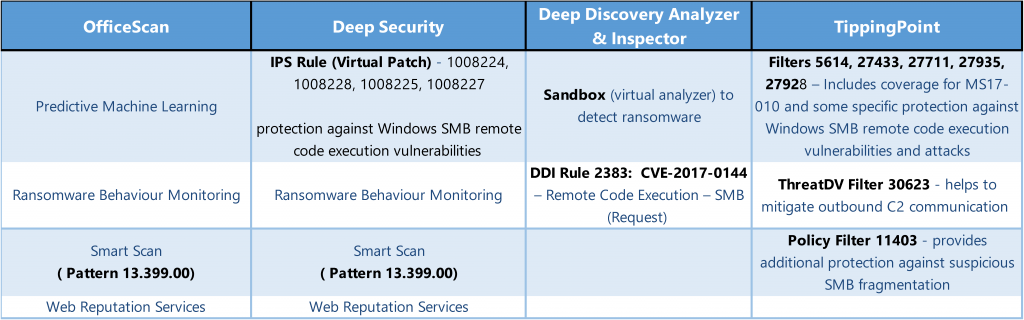
You may have heard over the weekend of the recent attacks of ransomware called WannaCry, which has targeted almost 200,000 computers across 150 countries. While a killswitch has been found to help lessen the spread of WannaCry, many still believe that a new strain of WannaCry will soon come out which will bypass this quick fix. Microsoft […]
