Backup and Disaster Recovery

Risks to business data are everywhere.
Deleted files, your backup failed you, server crashed, hardware broke, and the most dreaded thing, you lose your entire site – these disasters, natural, human error or system disaster would definitely lead to a loss way beyond simply losing those data. It is literally cutting off our lifeline: financial losses, break on productivity, fines, remediation cost, even reputation loss. Think about it: Can we even afford to lose any of it?
It is not a matter of when your business will become a victim; it’s just a question of when.
That’s why we believe that it’s time to re-imagine enterprise backup and disaster recovery and take advantage of the available new architectures and technology to transform it into an all-in-one solution that lets you go beyond a simple Backup solution.
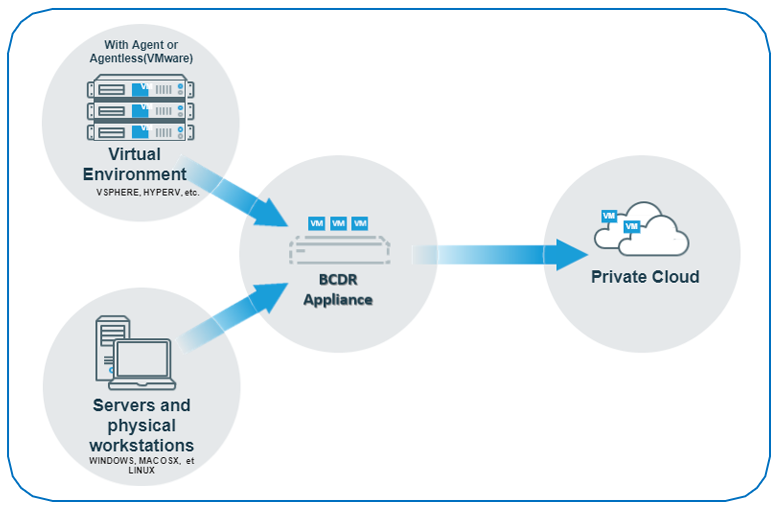
The solution supports a wide variety of systems – both physical and virtual environment – and is very efficient when it comes to backing things up. All backup and disaster recovery strategies begin with local backups on the appliance where each backup functions as a recovery point for the protected asset. After you’ve backed up your assets, you can recover individual files, databases, file systems, entire machines, or use the instant recovery features to recover critical machines in minutes. Every recovery point is in a fully constructed state and any point can be deleted without resetting a chain. With this, you can backup as frequent as every 5 mins which means lower RPO. You use or restore any backup points, no reconstruction required. You have the freedom to choose which want to keep or remove. And since all recovery points are 100% constructed, it’s good for supporting instant virtualization.
We can customize your backup strategy to meet the recovery point objectives (RPOs) and recovery time objectives (RTOs) required for your business continuity plan. We can customize the schedules to create backups at the desired frequency and use retention policies to control the number of recovery points available on your appliance. Use backup copies stored on an off-site target for long-term retention and disaster recovery.
Our Cloud is purpose-built for security, speed and reliability. The entire synchronization, storage, and replication processes is encrypted (AES-256-bit encryption). This is an end-to-end solution, and storage isn’t the sale price. Time based retention costs are set per customer and disaster recovery don’t cost extra, it’s part of the solution.
With this entire solution, business continuity is possible. If something happens with your end system, say your pc or the server, all the data gone, system out, you can use the data from the appliance to virtualize your machine or virtualize on other machines if your current one broke down. If even your appliance malfunctions, you can still source the cloud to virtualize a computer to restore your entire infrastructure, even if your office is under the water. The virtualization is not being run by the device, the cloud provides the computing power.
We’ll work on your entire solution, your business continuity, so you can have multiple ways to get your data back. And that’s what is needed in a backup and business continuity strategy.
To learn more about improving your business, contact us at 8893-9515 or fill out the form below!
By clicking “Submit,” you agree to our Privacy Policy and consent to the collection and use of your personal information as described therein.
