Protect your network from vulnerabilities from your medical devices

Business security is always evolving. This is even more so for the healthcare industry that handles confidential patient data daily. The pandemic has had an impact on how we handle remote work and its security risks. However, threats can get inside your network not only through your remote workforce, but even medical devices also carry their risks.
This is where solutions like Trend Micro’s Portable Security (TMPS) can help. They can drastically improve the security of standalone computers like medical devices against threats like malware. It provides improved OT visibility for your Team and eliminates problematic shadow IT & OT solutions. Below are a few examples of in which TMPS can help bridge the gap in your network security:

No internet, no problem
Medical Devices are connected to computers solely used to run the machine. This is why many have the impression that since its not connected to the internet, it cannot be attacked. However, this is not true as if anyone with an infected device (like a cellphone or USB) connects to it for whatever reason, this can become an entry point to your network when accessing its data.
Slowing down the device
The computers used to run medical devices are usually just enough to run the machine. One major issue machine technician state is that installing a security solution into the machine will slow down the work. Normal antivirus or malware protection solutions used for normal business assets will not cut it for specialized devices.

Little to no visibility
The IT team of many healthcare organizations have little to no visibility on medical devices. With no security solutions in place in these endpoints, it is hard to monitor logs or events that may have happened when an attack happens. Tracing an attack becomes a nightmare considering the number of devices it could have originated from.
One solution for your Healthcare organization
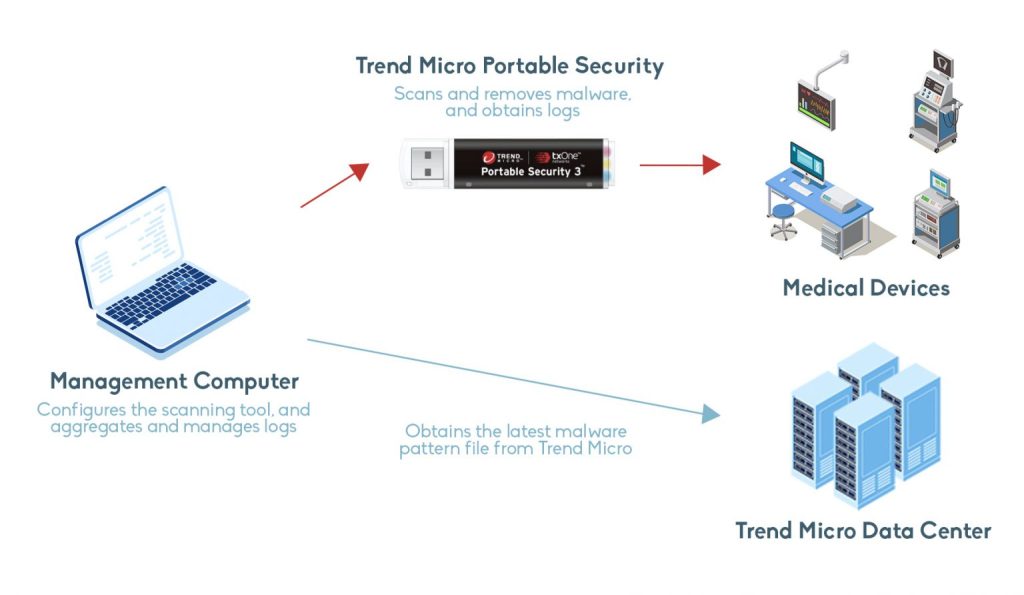
TMPS solves these issues through its portable and installation-free endpoint security. TMPS works by first updating a portable USB where the solution is then updated with the latest security database. Once it is updated, you can then connect it to the devices or computers that you wish to scan or audit check. It is simple enough that you do not need any IT background to use, a plug and play solution. The device information and updates can also be monitored by your IT Team to send updates to policies or can send reports and actions taken for threats.
If you are interested in learning more on how the solution works. Contact us here by filling out the form below, and we would be glad into further detail with your team!
By clicking “Submit,” you agree to our Privacy Policy and consent to the collection and use of your personal information as described therein.
