2018 Security Review: Looking at Old and New Threats to be aware of in 2019
Cybersecurity is something all companies big and small need to pay attention to as more attacks are becoming increasingly more popular. With company data being a corner stone of a business, it is no wonder attacks are becoming more frequent, if they can take your data then they can profit, its as simple as that. […]
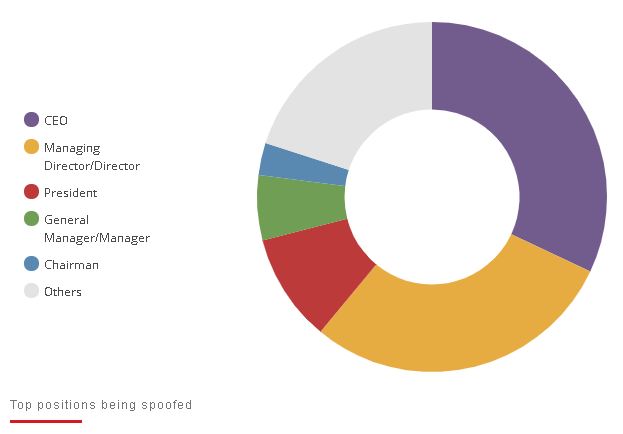
Security Tips: Different Business Email Compromise (BEC) Schemes to Watch Out For
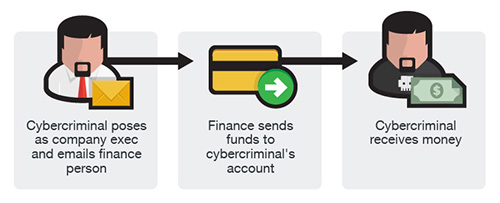
Business Email Compromise (BEC) Schemes In the past few years, millions of dollars have been lost to fraudsters and scammers. However, not all have been lost through malware attacks such as ransomware. Business email compromise (BEC) schemes are sophisticated attacks focused mostly on companies who do wireless transfers frequently. The FBI have estimated that nearly […]
