Are you thinking of switching or experiencing the simplicity of the Meraki Dashboard? Or are you a current Meraki user looking to expand your Meraki lineup? You’re in luck! For a limited time only, Meraki will be running a “First Year on Us” promo.
For a limited time only, any customer that purchases a new Cisco Meraki cloud management license for 3 years or more will get an additional year added at no extra cost! The extra 365 days are added automatically in the dashboard. No further steps required.
First Year On Us is available globally. License renewals do not qualify for this promotion.
Why Cloud Networking and the Meraki Dashboard
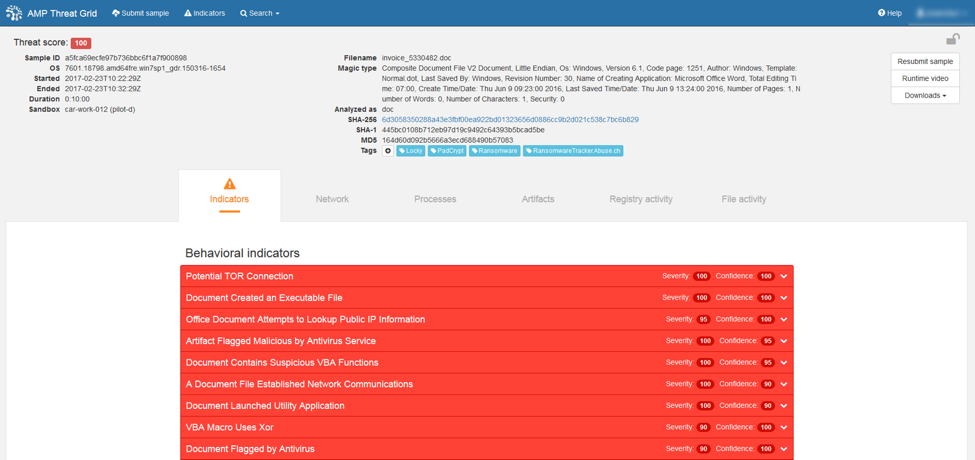
Meraki is a powerful tool that businesses can use to manage their network infrastructure efficiently and effectively. It provides a user-friendly interface that enables IT administrators to monitor and control their network from anywhere, at any time.
One of the main benefits of using Meraki is its ease of use. The dashboard is designed to be intuitive and straightforward, with a simple drag-and-drop interface that makes it easy to configure and manage network devices. This means that even non-technical staff can quickly learn how to use it.
Another advantage of using Meraki is its scalability. It is designed to work with networks of all sizes, from small businesses to large enterprises. As your business grows, you can easily add new devices and expand your network without having to worry about compatibility issues or other technical challenges.
Meraki also provides comprehensive network visibility and analytics. It allows you to monitor your network in real-time, so you can quickly identify and troubleshoot any issues that arise. Additionally, it provides detailed analytics and reports that can help you make informed decisions about your network infrastructure.
For more information about this promo, you may reply to this email or directly call us at 893-9515 and we would be happy to help!