With the suddenness of the declaration of the ECQ, most companies were unable to give their workforce the tools that they may have needed to work effectively at home. This left many employees to find their own ways to complete the tasks that they do on a daily basis at home. Many of which ended up using their own devices and installing the apps from work or apps and connecting to thru the company VPN.
Client Challenges: Unsecured Personal Devices connecting to Corporate VPN
One of our customers from the Public Sector encountered this dilemma during the start of the ECQ. They have about 500 employees who need to Work From Home (WFH). They were unable to give all employees resources in which to accomplish their tasks so opted to allow employees to use their personal devices. However, the Infosec Team is concerned that malwares from the personal devices could enter thru the VPN connections.

Solution: CT Link Managed Endpoint Security

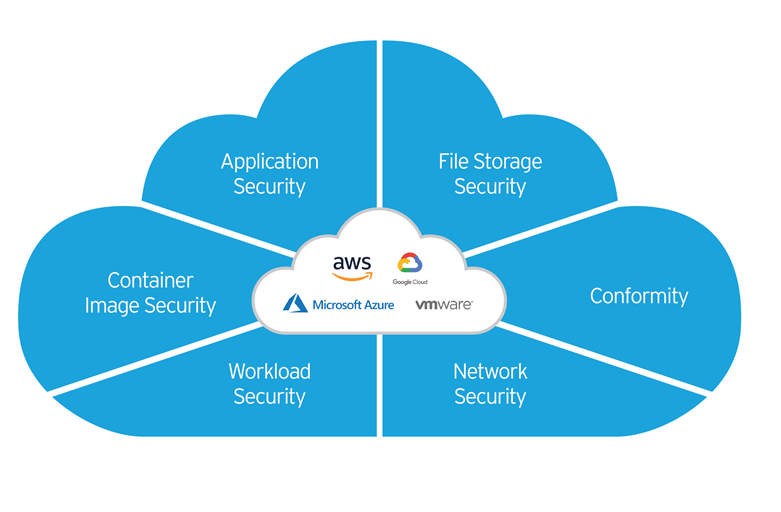
As a CT Link managed service customer, we deployed Trend Micro’s Worry-Free Business Security Services (WFBSS), which is a cloud-based Endpoint Security Solution. We provided the link for installing of Trend Micro Agents to end users and assisted them in deploying this on their endpoint devices.
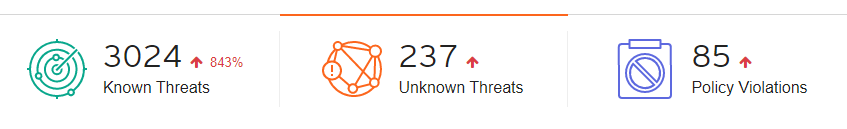
As a cloud-based solution, we were able to be with them every step of the way during this process and helped with problems that occurred during installation of some devices while also monitoring the threats found by WFBSS. This has proved as an effective measure for them as presently WFBSS has detected over 3,000 suspicious and malicious activities from the endpoints.
Security as a Service

Having Managed Services for security helped our client worry less about the security from personal devices connecting into their network and freed up their time to concentrate on other important tasks at hand during the ECQ. This meant that we handled the troubleshooting of the installations of the endpoint devices and monitoring of malicious activities reported by WFBSS. This service is also not reserved for only enterprise accounts as our services are actually very beneficial as well to small and medium businesses that do not have their own dedicated IT team. Below are a few key features in which you can expect to get when subscribed to our managed services:
- Keep outside threats like malware from getting in and sensitive data from going out
- Filtering potentially dangerous or inappropriate websites
- Preventing phishing and social engineered attacks from getting to your users
- As a cloud-based solution, support is done remotely
- Supports WFH setups to ensure your network is safe
- Ease of deployment with little to no IT skills required
- Centralized monitoring through one dashboard accessible through the cloud
If you are interested in learning more about our CT Link managed services or WFBSS, contact your CT Link AM or reply to this email and we will get back to you as soon as possible!